Almost all of us are email subscribers of some sort. From newsletters to promotional emails, we get one or more of these emails in our...
Key Takeaways
- BEC attacks succeed through impersonation and social engineering alone, bypassing most technical security controls that focus on detecting malicious code or suspicious links.
- BEC attackers research targets extensively using LinkedIn, company websites, and public records before crafting convincing impersonation emails tailored to real business relationships.
- Authentication protocols (SPF, DKIM, DMARC) reduce domain spoofing, but employee training and financial verification procedures are equally critical because BEC specifically exploits human trust.
Your finance manager gets an email from the CEO asking for an urgent wire transfer before the end of the day. The message uses the CEO’s name, references a real deal that’s in progress, and asks for discretion. It feels serious and time-sensitive. The manager processes the transfer, and only later learns the CEO never sent that email.
That’s business email compromise. And it’s now the most financially damaging form of cybercrime. The FBI’s Internet Crime Complaint Center reported several billion dollars in BEC losses in 2023 alone, and the real number is likely higher because many incidents go unreported. What makes BEC so dangerous is how simple it is. There’s no malware attachment. No obvious exploit. Just a well-researched, highly convincing impersonation.
Understanding what business email compromise is, how these attacks unfold, and which defenses actually work gives organizations a better chance of protecting their financial accounts, sensitive data, and core operations from the kind of loss BEC is designed to cause.
What Is a Business Email Compromise?
Business email compromise is a sophisticated fraud scheme where attackers impersonate trusted individuals, including executives, vendors, business partners, and colleagues, through email to manipulate employees into taking actions that benefit the attacker financially or informationally.
Attackers don’t need technical skills to breach systems; they need enough information about an organization’s structure, relationships, and processes to craft believable impersonation emails directed at employees with authority to transfer funds, share data, or change account information.
Generic phishing sends identical messages to thousands of random recipients, hoping some percentage will fall for broad deception. BEC is the opposite: one carefully researched message, sent to one specific target, impersonating one specific trusted person, referencing real organizational context.
This targeted approach is what makes BEC both more effective and more costly than generic phishing. It works because organizations run on email-based trust. Employees process payment requests from executives, respond to vendor invoice changes, and share information with attorneys or auditors without always being able to verify identities through other channels.
How Business Email Compromise Attacks Work
BEC attacks follow a structured methodology from initial research through fraudulent request execution.

Step 1: Target selection and research
Attackers identify organizations and specific individuals worth targeting, typically those with financial authority (CFOs, accounts payable managers), access to sensitive data (HR managers, executive assistants), or control over vendor relationships.
Research sources include LinkedIn profiles showing organizational hierarchy, company websites identifying executives and their roles, press releases announcing partnerships and deals, social media revealing travel schedules and current priorities, and public financial filings showing company size and transaction volumes.
This research phase can last weeks. Attackers map reporting relationships, identify which employees process payments, understand vendor relationships, and look for upcoming events, such as acquisitions, audits, or tax deadlines, that provide credible pretexts for urgent requests.
Step 2: Account takeover or domain spoofing
Attackers gain the ability to send convincing messages through two main methods: account takeover and domain spoofing.
In an account takeover, attackers compromise a legitimate email account, often through phishing, credential stuffing, or purchasing breached credentials, and send BEC messages from the real address. These attacks are the most convincing because they come from genuine, trusted accounts.
When attackers don’t have account access, they rely on impersonation techniques. They may use display name spoofing, where the sender name appears legitimate even though the underlying email address is different. In other cases, they register lookalike domains such as company-inc.com or cornpany.com that closely resemble the real domain and can pass casual inspection.
Step 3: Social engineering and message crafting
Using gathered research, attackers craft messages that feel authentic. They reference real projects, real relationships, current business events, and the communication style of the impersonated individual. Messages are often brief and professional, long enough to be convincing, and short enough to avoid inconsistencies.
Step 4: Fraudulent request execution
The message delivers a request designed to be processed quickly with minimal verification: a wire transfer to a new account, an invoice payment to a changed bank account, employee payroll redirected to attacker-controlled accounts, or sensitive data forwarded for a seemingly legitimate reason.
Urgency and secrecy are common pressure tactics: “Process this before close of business today,” “Don’t go through the usual channels on this one,” “Keep this confidential until the deal closes.” These requests are designed to prevent the verification steps that would expose the fraud.
Common Types of BEC Scams
BEC attacks take several distinct forms, each targeting different organizational vulnerabilities.
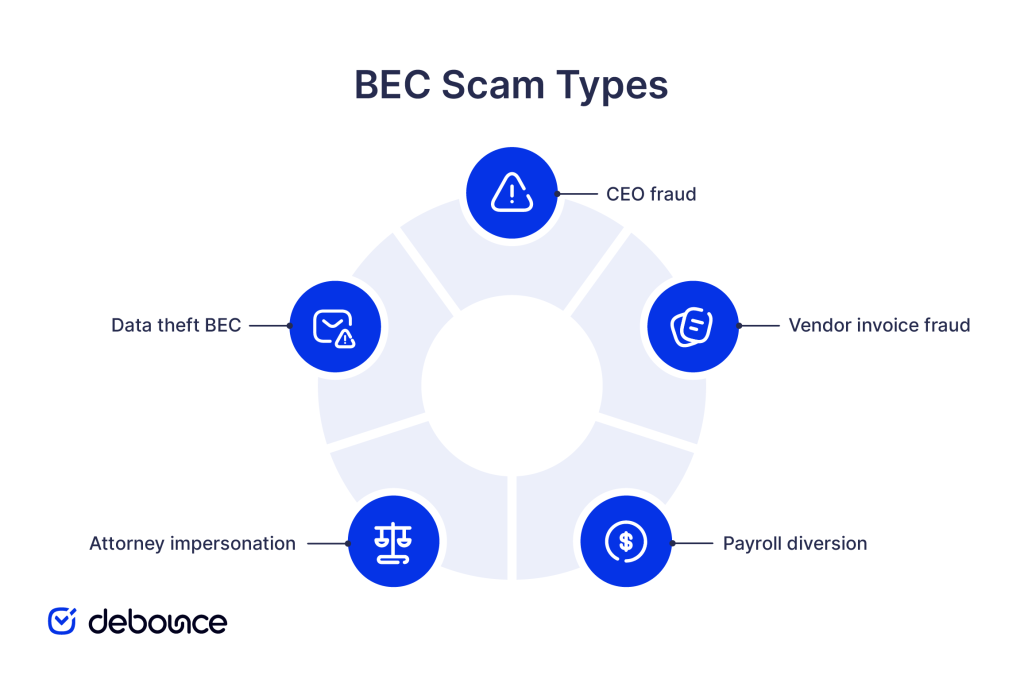
CEO fraud
The most well-known BEC variant, CEO fraud, involves attackers impersonating an organization’s chief executive to pressure lower-level employees into urgent action. A finance manager receives an email appearing to come from the CEO requesting an immediate wire transfer for a confidential acquisition, bypassing normal approval processes.
CEO fraud exploits the authority relationship between executives and employees. Most people don’t question direct requests from their CEO, particularly when accompanied by urgency and a request for discretion.
Vendor invoice fraud
Attackers impersonate a known vendor or supplier, informing the target organization that banking details have changed and requesting that upcoming payments be directed to a new account. Because the communication references real vendor relationships and ongoing business, it appears routine.
This variant is particularly effective because invoice processing involves regular communications with external parties, making it harder for accounts payable teams to verify every change through secondary channels.
Payroll diversion
HR departments receive emails appearing to come from employees requesting payroll direct deposit changes to new bank accounts. If processed, the employee’s next paycheck, or multiple paychecks, are routed to the attacker’s account rather than the employee’s.
These attacks target HR rather than finance, exploiting the routine nature of payroll change requests that HR teams process regularly.
Attorney impersonation
Attackers impersonate attorneys, law firms, or legal counsel handling sensitive matters (mergers, acquisitions, compliance issues, or litigation) and request urgent financial transfers or confidential information. The legal authority framing reduces recipients’ inclination to question or verify.
Requests often emphasize legal confidentiality requirements to discourage employees from consulting colleagues who might raise questions.
Data theft BEC
Not all BEC attacks seek money. Some target sensitive data: W-2 forms containing employee Social Security numbers and salary information, intellectual property, customer databases, or confidential business strategy documents.
Data theft BEC often comes before financial fraud. When attackers steal employee information, such as payroll details or direct deposit data, they can later use it to redirect salaries or benefits payments. At the same time, internal documents, contact lists, and communication patterns give attackers the insight they need to craft more believable impersonation emails in future attacks.
Warning Signs of a BEC Attack
BEC messages are designed to look legitimate, but specific patterns reveal their true nature on careful inspection.

Sender and domain inconsistencies:
- Displayed name doesn’t match the actual email address when you hover or click to inspect
- Domain uses subtle variations: company-inc.com, cornpany.com, company.co instead of company.com
- Free email providers (Gmail, Yahoo) are used for supposedly executive communications
- Reply-to address differs from the From address, redirecting responses to attacker-controlled accounts
Language and tone anomalies:
- Writing style, vocabulary, or formality level inconsistent with how the supposed sender normally communicates
- Generic salutations (“Hello,” “Hi Team”) from executives who typically use your name
- Slightly awkward phrasing that doesn’t match native speaker patterns
- References to relationships or projects that feel slightly off or are generically described
Unusual financial requests:
- Requests to wire funds to new, unverified accounts
- Vendor payment instructions with changed banking details
- Requests to purchase gift cards and share codes (a near-universal BEC warning sign)
- Urgency around transactions that normally follow established approval processes
Urgency and secrecy pressure:
- “Must be done today,” “before close of business,” or other artificial time pressure
- Requests to bypass normal approval procedures
- Instructions to keep the request confidential until the transaction completes
- Discomfort or discouragement when you suggest verifying through standard channels
Unusual request context:
- Financial requests from executives who don’t normally initiate payments directly
- Vendor change requests without prior notice or context
- Attorney communications about matters you weren’t previously aware of
- Requests received when the supposed sender is known to be traveling or unavailable
Maintaining clean, verified contact lists and using reliable email verification tools helps organizations identify when messages arrive from addresses that don’t match established contact records, which is an early signal of potential BEC activity.
How to Prevent Business Email Compromise
Effective BEC prevention requires layered controls across technical systems, employee behavior, financial processes, and organizational policy.
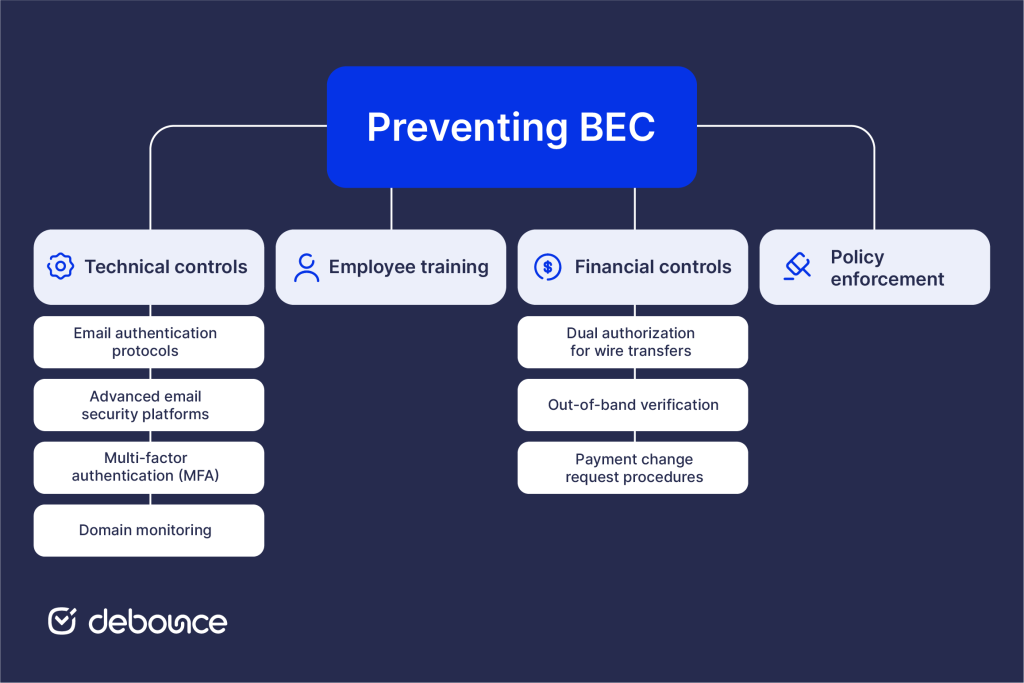
Technical controls
No single technical solution stops BEC on its own, so organizations must combine authentication, monitoring, and access controls to reduce risk.
Email authentication protocols
Proper configuration of SPF records, DKIM, and DMARC at an enforcement policy significantly reduces direct domain spoofing, preventing attackers from sending unauthenticated messages that appear to originate from your exact domain. DMARC p=reject ensures that unauthenticated messages claiming to be from your domain don’t reach recipients, protecting both your employees from incoming spoofing and your customers from attackers impersonating your organization.
Advanced email security platforms
AI-powered email security tools monitor how people typically communicate and look for activity that falls outside those patterns. For example, they may flag emails that differ noticeably from a sender’s usual tone or wording, or login attempts from unfamiliar locations or IP addresses. Because these systems analyze behavior rather than just scanning for known malicious links or attachments, they can detect well-crafted BEC attempts that traditional signature-based filters often fail to catch.
Multi-factor authentication (MFA)
Multi-factor authentication (MFA) on all email accounts helps prevent account takeover, which is one of the most convincing forms of BEC. When attackers gain access to a real employee’s inbox, their messages appear fully legitimate because they are sent from an authentic, trusted address. MFA adds a second verification step, so even if attackers steal a password through phishing, they still cannot log in and use the account to send fraudulent messages.
Domain monitoring
Register common lookalike versions of your organization’s domain, such as slight misspellings or hyphenated variations, to prevent attackers from using them. In addition, monitor domain registration activity for newly created domains that closely resemble your brand. Detecting these domains early can signal preparation for a BEC campaign and give you time to investigate or take defensive action before fraudulent emails are sent.
Employee training
Regular, scenario-based training focused on BEC equips employees to recognize subtle red flags that automated security tools may overlook. Employees should practice identifying:
- Display name spoofing vs. actual sending addresses
- Urgency and secrecy pressure tactics
- Unusual financial request patterns
- How to verify requests through secondary channels
BEC simulation exercises, where IT sends controlled fake BEC messages to test employee responses, identify training gaps, and build practical recognition skills more effectively than classroom instruction alone.
Financial controls
Financial safeguards ensure that even if a deceptive email reaches an employee, it cannot immediately trigger irreversible payment actions.
Dual authorization for wire transfers
Require two independent approvals for wire transfers above the defined thresholds. BEC attacks often exploit situations where only one person has the authority to release funds, making that individual a prime target for deception. Requiring dual authorization ensures that even if one employee is misled, a second review adds a critical safeguard before money leaves the organization.
Out-of-band verification
Establish a policy requiring phone verification, using known, pre-established phone numbers, for any payment instructions involving new accounts, changed banking details, or unusual amounts. Employees should never rely on contact information provided within the email itself when confirming these requests. A simple verification call through a trusted channel can stop many financial BEC attempts before funds are transferred.
Payment change request procedures
Establish a structured procedure for vendor banking change requests that includes several verification steps before any updates are approved. This should involve direct callback to established vendor contacts and waiting periods before processing. Routine processes for changes reduce attacker effectiveness.
Policy enforcement
Clear, written policies around financial authorization, payment change requests, and unusual data sharing requests give employees a framework for handling suspicious situations without feeling they’re questioning legitimate authority. Policies that explicitly state “we will never ask for urgent wire transfers by email alone” reduce the pressure that BEC attacks exploit.
Cleaning email lists regularly supports effective BEC detection, as high bounce rates and poor sender reputation can weaken security filtering that helps catch suspicious messages.
The Bottom Line
Business email compromise succeeds because it exploits organizational trust rather than technical vulnerabilities. Attackers invest in research, craft convincing impersonations, and target the specific people and processes that handle financial transactions and sensitive data, without needing a single line of malicious code.
Prevention requires matching that sophistication with layered defenses: authentication protocols that prevent domain spoofing, MFA that blocks account takeover, employee training that builds BEC-specific recognition skills, and financial controls that require out-of-band verification before processing unusual requests.
Maintaining clean email infrastructure is part of your BEC defense posture. Use DeBounce to verify contact lists and reduce bounced emails that weaken sender reputation. When your contact data is accurate, and your authentication controls are properly configured, it becomes easier to detect messages that originate outside established vendor and partner relationships, making BEC attempts more difficult to execute successfully.