Spear phishing uses researched, target-specific information that makes messages appear trustworthy, bypassing generic spam filters and human instinct. Spear phishing attackers gather information...
Key Takeaways
- Email impersonation happens when an attacker sends messages that appear to come from a trusted person or organization, without needing to hack the real account.
- The three most common email impersonation methods are display name spoofing, lookalike domains, and compromised accounts.
- CEO fraud, vendor invoice scams, and fake customer support emails are the attack types that cause the most financial and reputational damage to businesses.
- When it comes to preventing email impersonation attacks, employee training and internal verification workflows are just as important as technical controls.
An email shows up in your finance manager’s inbox: it’s from the CEO, asking for an urgent wire transfer. The sender’s name is correct, and the tone sounds right. The only problem is that the CEO never sent it.
This is email impersonation, one of the most common and costly forms of cybercrime targeting businesses today. Unlike malware or complex hacking attempts, impersonation attacks don’t rely on advanced technical tricks. Often, all it takes is a believable sender name and a busy recipient who doesn’t have time to double-check the details. Email spam statistics show that a significant share of malicious email traffic involves some form of identity deception, which makes this a risk every business needs to understand and actively defend against.
This guide explains how email impersonation attacks work, what they typically look like in real situations, and the practical steps businesses can take to prevent them.
What Is Email Impersonation?
Email impersonation is the practice of sending emails that falsely appear to originate from a trusted sender, like a colleague, executive, vendor, or well-known brand, with the intent to deceive the recipient into taking a harmful action. That action might be transferring money, sharing login credentials, clicking a malicious link, or disclosing sensitive information.
What separates impersonation from ordinary spam is the deliberate targeting. Impersonation attacks are created to exploit an existing relationship or expectation of trust. The attacker isn’t trying to sell something, but they’re trying to become someone.
Crucially, email impersonation doesn’t require the attacker to have access to the real sender’s account. In most cases, they simply fabricate the appearance of legitimacy using technical tricks or social engineering. That’s what makes it so accessible to attackers and so dangerous for organizations of any size.
How Email Impersonation Works
Attackers use three main methods to make their emails appear to come from someone else.
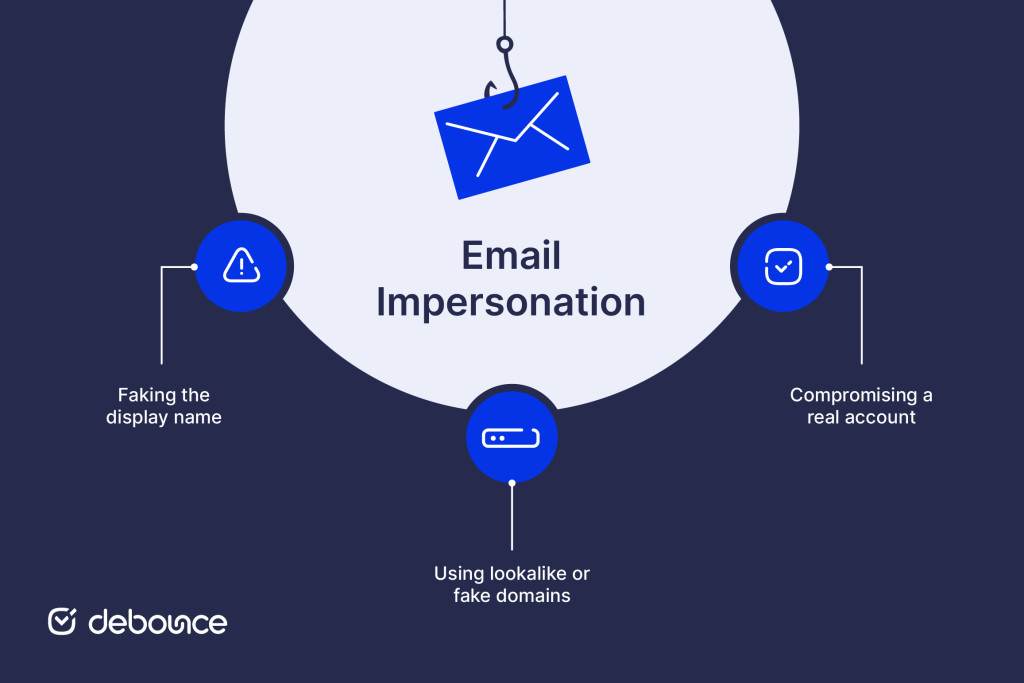
Faking the display name
Email clients like Outlook and Gmail show the sender’s display name prominently, while the actual email address is often hidden unless the recipient clicks to expand it. Attackers exploit this by setting their display name to “John Smith, CEO” while sending from a completely unrelated address like [email protected]. Many recipients never check the address behind the name.
Using lookalike or fake domains
A more advanced tactic involves registering a domain that looks almost identical to the real one used by a company. If your organization uses acmecorp.com, an attacker might register something like acme-corp.com, acmecorp.net, or acrnecorp.com, where a single character is subtly changed.
With a quick look, these addresses appear legitimate. Because the domain itself exists and can send email normally, messages from it often pass basic sender checks. This makes the attack harder to spot than simple display name spoofing. The technique is closely related to email spoofing, and the two are often used together.
Compromising a real account
When an attacker gains access to an actual email account through phishing, credential theft, or a data breach, they can send messages directly from the legitimate address. This is the hardest form of impersonation to detect because the emails genuinely come from where they claim to. Strong authentication controls and monitoring are the primary defenses here.
Common Types of Email Impersonation Attacks
Impersonation attacks follow predictable patterns. Understanding the most common scenarios helps teams recognize and respond to them faster.
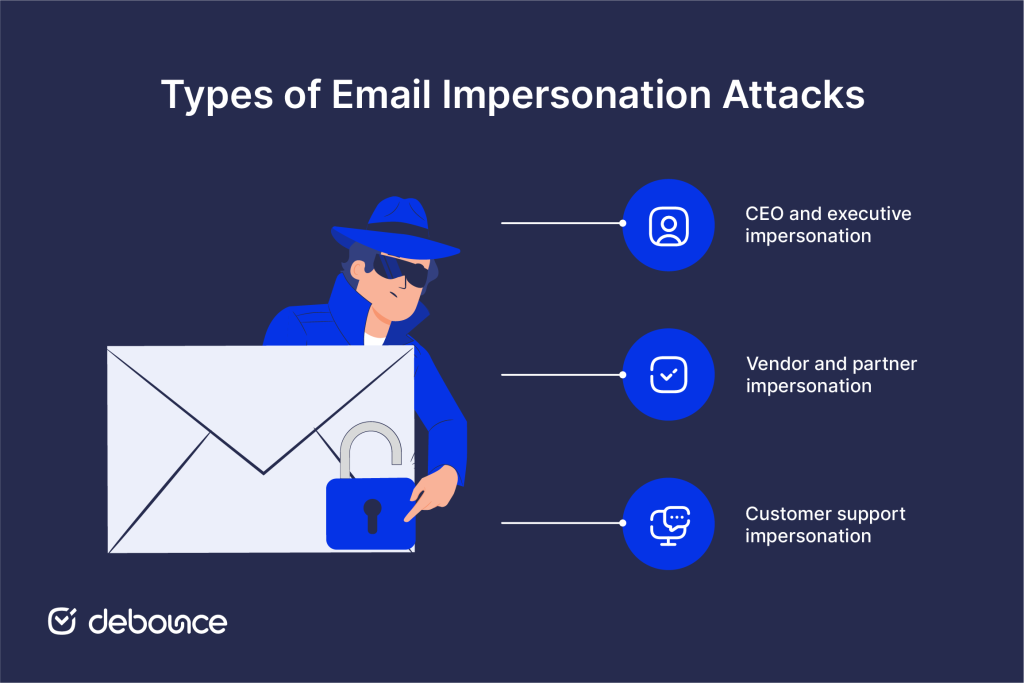
CEO and executive impersonation
Also known as business email compromise (BEC) or CEO fraud, this attack involves an impersonator posing as a senior leader, typically the CEO, CFO, or another executive, to pressure an employee into taking an unauthorized action.
The targets are usually employees who have authority over financial transactions or access to sensitive data, such as finance teams, HR, payroll administrators, and executive assistants. The requests are designed to feel urgent and confidential: “Don’t loop in anyone else on this, just process it before market close.”
Common objectives include fraudulent wire transfers, gift card purchases, W-2 or payroll data requests, and changes to direct deposit details. The FBI’s Internet Crime Complaint Center (IC3) has consistently identified BEC as one of the highest-loss cybercrime categories globally, with billions lost annually.
Vendor and partner impersonation
In this scenario, attackers impersonate a known supplier, contractor, or business partner. They typically gain enough information about the relationship, often through publicly available sources or a prior breach, to make their emails credible.
A typical attack involves sending a spoofed invoice that looks identical to the vendor’s real invoices, with one change: the bank account number. The recipient processes what looks like a routine payment, and the funds land in the attacker’s account. Recovery is difficult and often impossible (by the time the fraud is detected).
This type of attack is particularly dangerous because it exploits established trust. The recipient isn’t being asked to do anything unusual, just pay a vendor they work with regularly.
Customer support impersonation
Attackers pretend to be customer support staff from a company or service. Instead of trying to trick employees inside the organization, they target regular users or customers of that service. They send emails that appear to come from a well-known company’s support department (a bank, software provider, or e-commerce platform), warning the recipient of an account issue that requires immediate action.
The goal is typically credential theft. The email links to a convincing fake login page where the victim enters their username and password, handing them directly to the attacker. This approach is also connected to pharming techniques, where users are redirected to fake websites designed to look legitimate. Stolen credentials can then be used for account takeover, resold, or used to launch further attacks.
How to Prevent Email Impersonation
Effective email impersonation protection requires a layered approach. No single control is sufficient: technical safeguards, human awareness, and internal procedures all need to work together.

Email authentication protocols
Three email authentication protocols that work through DNS help prevent domain impersonation. These protocols should be set up for every domain your organization uses to send email, not only the main domain but also any secondary or inactive ones that still belong to your organization.
- SPF (Sender Policy Framework): A DNS record that lists the mail servers permitted to send email using your domain. When a receiving server checks an incoming message, it verifies whether the sending server is on the approved list. If not, the message can be flagged or rejected.
- DKIM (DomainKeys Identified Mail): Adds a cryptographic signature to outgoing messages that the receiving server can verify. It confirms that the email genuinely originated from your domain and hasn’t been altered in transit.
- DMARC (Domain-based Message Authentication, Reporting & Conformance): Builds on SPF and DKIM by letting domain owners specify what should happen when a message fails authentication: monitor only, quarantine it, or reject it. DMARC also sends reports to the domain owner showing which servers are sending email using the domain, which helps monitor and control authorized sending sources.
Setting DMARC to a “reject” policy is the strongest protection, but organizations typically start with “monitor” to understand their legitimate email traffic before enforcing strict rules. Email encryption adds another layer by protecting message content in transit and at rest.
Employee training and awareness
Technical controls block some impersonation attempts, but many attacks are designed to slip past automated filters and land in real inboxes. That is why staff training is essential.
Employees at every level should understand:
- How to verify a sender’s actual email address, not just the display name. On most clients, hovering over or clicking the sender name reveals the underlying address.
- The warning signs of urgency-based manipulation, including messages that pressure them to act quickly, skip normal approval steps, or keep the request confidential from management.
- What to do when a request feels unusual, even if it appears to come from a known contact. A quick phone call to verify is always faster than recovering from fraud.
- How lookalike domains work and what to look for when an address seems slightly off, such as transposed letters, added hyphens, or a different top-level domain.
Training should be practical and repeated, not a one-time exercise. Simulated phishing campaigns, where IT or security teams send fake impersonation emails to staff, are one of the most effective ways to reinforce awareness and identify who needs additional guidance.
Security tools and filters
Purpose-built security tools provide detection and blocking capabilities that basic email filtering doesn’t cover.
- Anti-phishing and anti-spoofing filters scan incoming messages for characteristics associated with impersonation, such as mismatched domains, suspicious header data, lookalike sender addresses, and known malicious links.
- Email gateway solutions sit between the internet and your mail server, applying additional checks before messages reach employee inboxes.
- Domain monitoring services alert you when new domains that closely resemble yours are registered, giving you early warning of a potential lookalike domain attack before it’s used.
- DMARC reporting tools turn raw DMARC reports into readable dashboards, making it easier to spot unauthorized senders using your domain.
Working with established email security companies can help you assess which tools are appropriate for your organization’s size, infrastructure, and risk profile.
Verification procedures
The final layer of defense is procedural: internal workflows that require out-of-band verification for high-risk requests, regardless of how legitimate the email looks.
Effective verification procedures include:
- A strict policy that no wire transfer, payment change, or sensitive data request is approved based on email alone. Any such request, regardless of who it appears to come from, must be confirmed via phone call or in person using a contact number from your internal directory, not one provided in the email.
- Dual-approval requirements for financial transactions above a defined threshold. Having two separate people reviewing and approving a payment makes it significantly harder for a single impersonation email to succeed.
- A clear escalation path for suspicious emails. Employees should know exactly who to contact and how when they receive a message that seems off, and they should feel safe reporting it without fear of embarrassment.
These procedures cost nothing to implement and are often more effective than technical controls for stopping socially engineered attacks.
What to Do If You’re a Victim of Email Impersonation
If you discover that someone is impersonating your organization or that an employee has fallen victim to an attack, act quickly. The first hours matter.

Immediate response steps:
- Contain the damage: If a payment was made, contact your bank immediately to attempt a recall. Financial institutions have limited windows to intervene, so speed is essential.
- Preserve evidence: Don’t delete the impersonating emails. Save full message headers, screenshots, and any related correspondence. This documentation is essential for reporting and any subsequent investigation.
- Identify the scope: Determine whether the attack targeted one person or multiple accounts, and whether any sensitive data, such as credentials, financial records, or personal information, was accessed or shared.
- Reset compromised credentials: If any accounts were accessed, force password resets and revoke active sessions immediately. Enable multi-factor authentication if it wasn’t already active.
Reporting and notification:
- Report the incident to your country’s relevant cybercrime authority. In the US, that’s the FBI’s IC3 (ic3.gov).
- If customer data was involved, consult your legal team about breach notification obligations under applicable data protection regulations (GDPR, CCPA, and others, depending on your jurisdiction).
- Notify affected partners or vendors if their identities were used in the attack, as they may be facing similar threats.
- Inform your email provider and, if applicable, request that the impersonating domain be reported for abuse.
After the immediate response, conduct a post-incident review: how did the attack get through, what controls failed, and what changes are needed to reduce the risk of recurrence. Clean up email infrastructure and security configurations as part of that review.
Protect Your Domain Before Attackers Use It Against You
One often-overlooked aspect of impersonation protection is the quality and security of your own outbound email practices. Organizations with poorly maintained email lists, unverified contact databases, or misconfigured sending infrastructure are more vulnerable, both to having their domain abused and to inadvertently sending mail that inbox providers treat with suspicion.
Email verification is part of a sound email hygiene practice that supports your broader security posture. DeBounce validates email addresses without sending any messages, removing invalid, disposable, and high-risk addresses from your lists so your domain builds a consistent, trustworthy sending reputation. A domain with a strong reputation is harder to impersonate convincingly and easier to defend when you report abuse.
Run your email list through DeBounce to make sure your outbound sending is clean, verified, and working in your favor.
Build Defenses That Match the Threat
Email impersonation succeeds because it targets trust: the trust employees place in a familiar name, the trust customers place in a known brand, the trust that makes email a functional tool for business. Attackers don’t need to break through firewalls when they can simply pretend to be someone you already trust.
The defenses covered in this guide: SPF, DKIM, and DMARC authentication; staff training; security filtering tools; and internal verification procedures, address both the technical and human dimensions of the problem. None of them is sufficient alone, but together they make impersonation attacks significantly harder to execute and easier to catch.
Start with your authentication records. If your domain isn’t publishing a DMARC policy yet, that’s the single most impactful technical step you can take right now. Pair it with a staff training session and a clear payment verification procedure, and you’ll have closed the gaps that most successful impersonation attacks exploit.