Are your emails constantly landing in spam folders or being rejected? Your domain's multiple SPF records might be the cause of the issue. Unfortunately, despite...
Key Takeaways
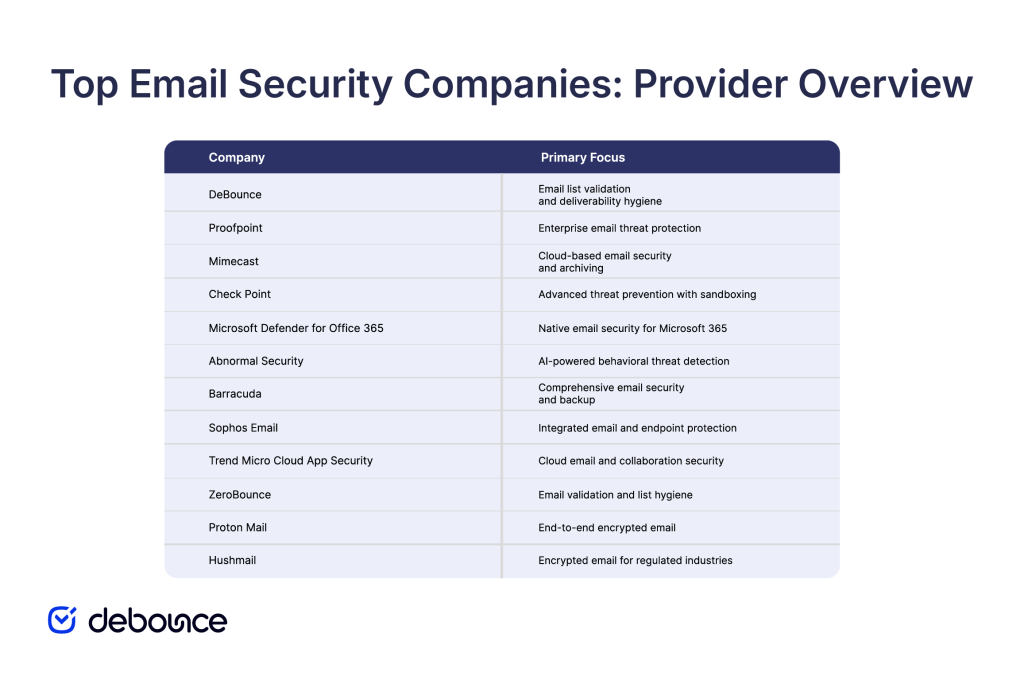
- Enterprise platforms protect against advanced persistent threats and BEC, privacy providers focus on encryption, and hygiene services prevent delivery failures and list contamination.
- The right email security company depends on organization size, threat landscape, email platform, and whether you prioritize threat detection, privacy, or deliverability.
- Comprehensive email security combines threat detection platforms with email authentication, list validation, and user training rather than relying on a single solution.
Over 90% of cyberattacks start with email. Phishing messages, malware attachments, ransomware delivery, and Business Email Compromise scams all arrive through the same channel businesses rely on for daily communication.
Email security companies specialize in protecting organizations and individuals from these email-based threats. Their solutions range from enterprise platforms that scan every incoming message for sophisticated attacks to privacy-focused email providers that encrypt messages end-to-end, and supporting services that maintain list quality to prevent bounced emails and delivery failures.
No single solution fits every use case. For example, a Fortune 500 company faces different threats and has different requirements than a solo consultant or privacy-conscious individual.
This guide explains what email security companies protect against, profiles twelve leading providers across different categories, and outlines key factors to consider when selecting email protection that matches your organization’s size, risk profile, and email infrastructure.
What Email Security Companies Protect Against
Email security companies defend against multiple categories of threats that exploit email as an attack vector.

Phishing attacks
Phishing messages impersonate trusted entities, like banks, colleagues, or service providers, to trick recipients into revealing credentials, clicking malicious links, or downloading malware. These attacks rely on social engineering rather than technical exploits, making them effective even against technically sophisticated users.
Advanced phishing variants include spear phishing (targeting specific individuals using researched personal information) and whaling (targeting executives and other high-value decision-makers).
Malware and ransomware
Email attachments and links deliver malware that infects systems, steals data, or encrypts files for ransom. Ransomware specifically locks users out of their systems or data until they pay attackers, causing operational disruption and financial loss.
Traditional signature-based detection struggles against new malware variants, requiring behavioral analysis and sandboxing to catch threats before they execute.
Business email compromise (BEC)
BEC attacks impersonate executives, vendors, or business partners to request wire transfers, payroll changes, or sensitive data. These attacks often involve no malware, just convincing impersonation and social engineering.
BEC causes billions in annual losses because attacks bypass traditional security tools that focus on detecting malicious code rather than fraudulent intent.
Email spoofing and impersonation
Spoofing forges sender addresses to make messages appear to come from trusted domains. Domain impersonation uses similar-looking domains (example.com vs examp1e.com) to deceive recipients.
These techniques support phishing and BEC attacks by making malicious messages appear legitimate at first glance.
Account takeover and credential theft
Attackers compromise email accounts through stolen credentials, then use those accounts to send phishing emails to contacts, access sensitive information, or conduct BEC attacks with genuine accounts.
Compromised accounts are particularly dangerous because messages come from real, trusted addresses that bypass many security filters.
Spam and unwanted bulk email
While less dangerous than targeted attacks, email spam still wastes time and clutters inboxes. High volumes of junk mail make it harder for users to spot important or legitimate messages. In some cases, spam also provides cover for malicious emails that slip through unnoticed.
Top Email Security Companies
Email security companies serve different markets and address different aspects of email protection. This overview highlights twelve providers across enterprise platforms, AI-powered detection, privacy-focused services, and email hygiene solutions.
DeBounce
Primary focus: Email list validation and deliverability hygiene
Audience: Marketing teams, sales organizations, agencies
DeBounce focuses on email list quality through validation services that identify invalid, risky, and temporary email addresses before sending. By removing addresses that would bounce, trigger spam filters, or belong to disposable domains, DeBounce helps maintain sender reputation and ensures marketing emails reach real, active recipients.
Email list validation prevents delivery failures caused by bad data rather than malicious threats, complementing security platforms by ensuring clean contact lists that support accurate threat detection and engagement metrics.
Proofpoint
Primary focus: Enterprise email threat protection
Audience: Large enterprises, Fortune 500 companies
Proofpoint provides comprehensive email security for large organizations, focusing on advanced threat protection, compliance, and data loss prevention. The platform uses threat intelligence, behavioral analysis, and sandboxing to detect and block sophisticated attacks.
Integration with Microsoft 365, Google Workspace, and other enterprise email platforms makes deployment straightforward for organizations already using these systems.
Mimecast
Primary focus: Cloud-based email security and archiving
Audience: Mid-market to enterprise organizations
Mimecast combines email security, archiving, and continuity services in a cloud platform. The solution protects against phishing, malware, and impersonation attacks while providing email backup and disaster recovery capabilities.
Mimecast’s unified platform appeals to organizations wanting security and archiving from a single vendor rather than managing multiple point solutions.
Check Point
Primary focus: Advanced threat prevention with sandboxing
Audience: Enterprise organizations with high security requirements
Check Point’s email security leverages threat intelligence from its broader cybersecurity platform to protect against zero-day threats, ransomware, and targeted attacks. Advanced sandboxing analyzes suspicious attachments and links in isolated environments before allowing them to reach recipients.
Organizations already using Check Point network security often extend their infrastructure to email protection for unified threat management.
Microsoft Defender for Office 365
Primary focus: Native protection for Microsoft 365
Audience: Organizations using Microsoft 365 and Exchange
Microsoft Defender for Office 365 provides integrated protection for organizations using Microsoft’s email and collaboration platforms. Built-in threat detection, anti-phishing, anti-malware, and Safe Links/Safe Attachments features protect against common and advanced threats.
The advantage for Microsoft-centric organizations is seamless integration and simplified administration through familiar Microsoft tooling.
Abnormal Security
Primary focus: AI-powered behavioral detection
Audience: Enterprises seeking advanced BEC protection
Abnormal Security uses behavioral AI to detect threats that bypass traditional security tools, focusing particularly on BEC, credential phishing, and vendor fraud. The platform analyzes communication patterns, relationships, and content to identify anomalies indicating attacks.
This behavioral approach catches socially engineered attacks that contain no malicious code or links, addressing the BEC problem that causes significant financial losses.
Barracuda
Primary focus: Complete email security for mid-market
Audience: Small to mid-sized businesses
Barracuda offers email security, backup, and encryption in packages designed for organizations without large security teams. The platform protects against phishing, malware, and spam while providing archiving and compliance features mid-market companies need.
Barracuda’s appeal lies in delivering enterprise-grade protection with simpler deployment and management suited to smaller IT departments.
Sophos Email
Primary focus: Integrated email and endpoint protection
Audience: Organizations using Sophos security products
Sophos Email Security integrates with Sophos’s broader endpoint and network protection, using shared threat intelligence to provide consistent defense across the infrastructure. Protection against phishing, malware, and data loss combines with sandboxing and URL reputation analysis.
Organizations already invested in the Sophos ecosystem benefit from unified management and correlated threat data across email and other security layers.
Trend Micro Cloud App Security
Primary focus: Cloud email and collaboration security
Audience: Enterprises using cloud email platforms
Trend Micro Cloud App Security protects Microsoft 365, Google Workspace, and other cloud collaboration platforms through API-based scanning that doesn’t require mail flow changes. Protection includes phishing detection, malware scanning, DLP, and compliance enforcement.
The API approach appeals to organizations wanting security without routing email through third-party gateways or altering existing mail flow configurations.
ZeroBounce
Primary focus: Email validation and deliverability
Audience: Email marketers, sales teams
ZeroBounce provides email validation services that identify invalid, risky, and low-quality email addresses before sending campaigns. Like DeBounce, ZeroBounce focuses on list hygiene and deliverability rather than threat detection, helping organizations maintain clean contact databases and healthy sender reputations.
Email validation services complement security platforms by ensuring accurate recipient data that supports effective threat analysis and campaign performance.
Proton Mail
Primary focus: End-to-end encrypted email for privacy
Audience: Privacy-conscious individuals and organizations
Proton Mail provides end-to-end encrypted email, where messages are encrypted on sender devices and decrypted only by intended recipients, preventing interception by third parties, including email providers. Headquartered in Switzerland, Proton operates under strong privacy laws.
Organizations and individuals prioritizing privacy over convenience choose Proton Mail for confidential communications that remain encrypted even if email servers are compromised.
Hushmail
Primary focus: Encrypted email for healthcare and legal
Audience: Healthcare providers, legal professionals
Hushmail offers an encrypted email designed for industries with strict compliance requirements like HIPAA (healthcare) and legal confidentiality rules. The platform provides encryption alongside features supporting compliance documentation and secure communication workflows.
Healthcare providers and legal professionals use Hushmail when industry regulations require encrypted email, but don’t need the broader security platform features enterprise solutions provide.
Choose the Right Email Security Company for Your Needs
Selecting the right email security company requires matching protection capabilities to your organization’s size, risk profile, email infrastructure, and compliance requirements.

Organization size and complexity
Enterprise organizations (1,000+ employees) typically need comprehensive platforms like Proofpoint, Mimecast, or Check Point that handle advanced threats, support complex email environments, provide detailed reporting, and integrate with existing security infrastructure.
Small to mid-sized businesses (10-500 employees) benefit from solutions like Barracuda or Microsoft Defender for Office 365 that deliver strong protection without requiring dedicated security teams for deployment and management.
Individuals and small teams seeking privacy more than enterprise threat protection choose encrypted providers such as Proton Mail or Hushmail, which prioritize confidentiality over advanced threat detection.
Threat landscape and risk profile
Organizations facing high BEC risk, including finance teams, executives handling wire transfers, and companies with complex vendor relationships, need behavioral AI platforms like Abnormal Security that specifically address social engineering and impersonation.
Industries with compliance requirements (healthcare, finance, legal) require solutions that support specific regulations such as HIPAA, FINRA, and GDPR, often including encryption, archiving, and audit capabilities.
Marketing-focused organizations that send high volumes of campaigns need email hygiene services like DeBounce to maintain list quality and prevent delivery failures that harm sender reputation and waste campaign budgets.
Email platform integration
Organizations using Microsoft 365 or Exchange often start with Microsoft Defender for Office 365 because it integrates natively without requiring mail flow changes or third-party gateways. Google Workspace users similarly benefit from solutions offering native Google integration or API-based protection that works within existing infrastructure.
Mixed environments or organizations using on-premises Exchange alongside cloud email need flexible platforms that protect across hybrid configurations.
Compliance and data protection
Industries with data residency requirements must ensure email data stays within specific geographic boundaries. This requires providers that offer regional data centres or on-premises deployment options. Organisations handling sensitive information also need strong encryption, data loss prevention, and archiving tools that support e-discovery and compliance audits.
Email hygiene as complementary protection
Regardless of which security platform you choose, maintaining clean email lists prevents delivery failures and supports accurate threat detection. Security platforms work best when trained on legitimate engagement data rather than distorted by bounces to invalid addresses.
Services like DeBounce complement security platforms by ensuring security for email marketers through validated, clean contact lists that reduce false positives, improve sender reputation, and prevent campaigns from being flagged due to high bounce rates.
The Bottom Line
Email security companies serve distinct purposes across threat detection, privacy protection, and deliverability management. Enterprise platforms like Proofpoint and Mimecast defend large organizations against sophisticated attacks, AI-powered solutions like Abnormal Security target specific threat categories like BEC, privacy providers like Proton Mail prioritize encryption over threat detection, and hygiene services like DeBounce maintain list quality that supports both security and deliverability.
The right choice depends on your organization’s size, threat landscape, email infrastructure, and whether you’re primarily concerned with advanced threat protection, privacy and encryption, or maintaining clean contact lists for reliable delivery.
Effective email security often requires layered protection: a threat detection platform to catch attacks, email authentication (SPF, DKIM, DMARC) to prevent spoofing, list validation to maintain data quality, and user training to recognize social engineering. No single vendor addresses every email security need.
So, assess your primary email security concern, and maintain email list quality as part of your security posture. Use DeBounce to verify contact lists regularly, removing invalid and risky addresses that cause bounces, hurt sender reputation, and distort engagement metrics security platforms use for threat detection. Clean lists support better deliverability, more accurate analytics, and stronger overall email security across all platforms.