How often do you interact with your email box? I bet pretty often. Whether you receive a critical business email, write a business partner, or...
Key Takeaways
- Spoofing fakes trusted identities to bypass filters and build credibility; phishing uses that credibility to manipulate victims into harmful actions.
- Most sophisticated phishing attacks use spoofing to appear legitimate, making the combination significantly more dangerous than either threat alone.
- Authentication protocols (SPF, DKIM, DMARC) address spoofing at the technical level; employee training and verification habits address phishing at the human level.
An email lands in your inbox from your IT department. It asks you to verify your login credentials through a link. The sender address looks correct, and the formatting feels familiar. Nothing seems out of place. You click the link, type in your password, and unknowingly hand it straight to an attacker who built a fake login page to mirror your company’s system.
That situation combines two separate threats working together: one made the message look legitimate, the other used that legitimacy to steal your credentials. Spoofing vs. phishing is one of cybersecurity’s most commonly confused distinctions. People often use the terms interchangeably, but they describe different things: one is a method, the other is a goal. Knowing which is which helps you apply the right defenses, recognize the right warning signs, and understand why attacks succeed even against technically aware targets.
What Is Spoofing?
Spoofing is the act of faking a technical identifier, such as an email sender address, domain name, website, caller ID, or IP address, to impersonate a trusted source.
In email contexts, spoofing manipulates the technical fields that control how sender information displays to recipients. Attackers forge the “From” address to show a trusted name and domain, register lookalike domains that pass casual visual inspection, or manipulate email headers so messages appear to originate from legitimate servers they don’t control.
Spoofing is primarily a technical attack. It manipulates systems and protocols so that a message, device, or website appears to come from a trusted source. While many attacks ultimately target people, spoofing itself works by exploiting weaknesses in how technology verifies identity.
It is also not limited to direct fraud. In many cases, the immediate objective is not credential theft or financial gain but reconnaissance, testing defenses, or preparing for a larger attack.
Primary spoofing types relevant to email:
- Display name spoofing: Showing “IT Support” as the name while using a random or unrelated sending address
- Domain spoofing: Sending from cornpany.com or company-support.com instead of company.com
- Direct email spoofing: Forging the From field to show a real, legitimate address using SMTP header manipulation
- Website spoofing: Creating replica sites at lookalike domains that capture entered credentials
What Is Phishing?
Phishing is a goal-driven social engineering attack that sends fraudulent messages to manipulate recipients into taking harmful actions, such as clicking malicious links, downloading malware, submitting credentials, or transferring funds. The name reflects the concept: casting a wide net and waiting for victims to take the bait.
Over 38 million phishing attacks were detected worldwide in 2024 alone, making up a quarter of all cybersecurity incidents detected that year. Phishing targets human psychology, exploiting instincts like trust, urgency, fear, and authority to override critical thinking and prompt immediate action before recipients pause to verify.
The defining characteristic of phishing is intent. Every phishing attack has a specific objective: harvest login credentials, deliver ransomware, divert a payment, steal personal data, or gain initial access to an organizational network. The message, channel, and deception technique are all in service of that objective.
Common phishing channels:
- Email phishing: The most common channel; fraudulent messages sent to broad audiences
- Spear phishing: Targeted email attacks using personalized research about specific individuals
- SMS phishing (smishing): Text messages containing malicious links or instructions
- Voice phishing (vishing): Phone calls impersonating trusted entities to extract information
- Social media phishing: Fraudulent messages, fake accounts, or malicious links through social platforms
- Fake websites: Landing pages designed to capture credentials entered by victims
What Is the Difference Between Phishing and Spoofing?
Spoofing and phishing are related but distinct. Understanding their differences across multiple dimensions clarifies both how attacks work and which defenses apply to each.
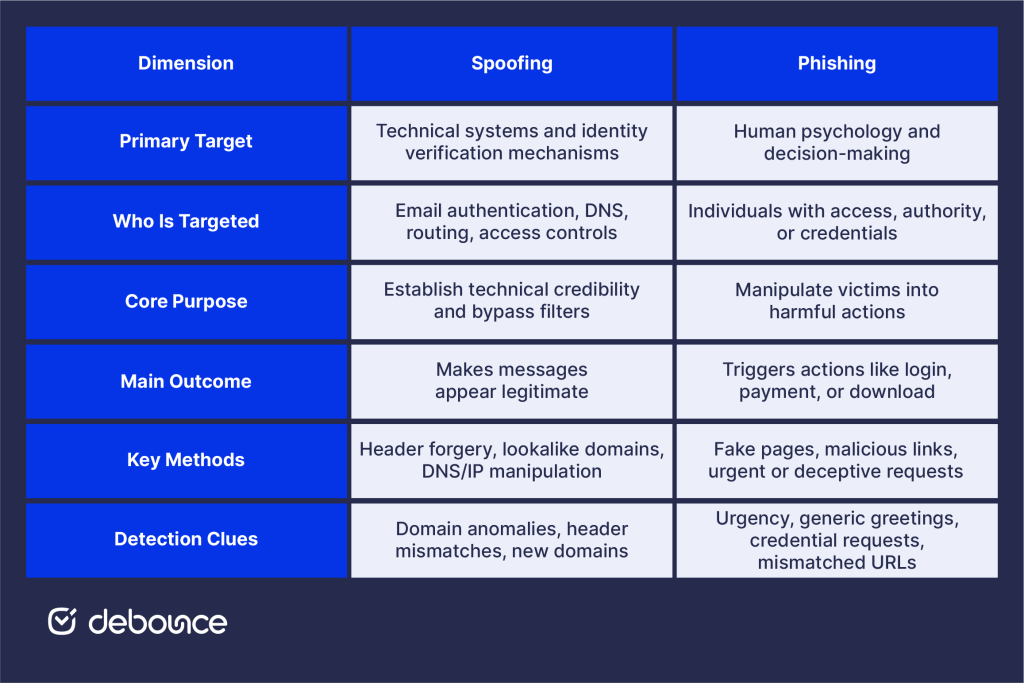
Primary targets
Spoofing targets systems and protocols first, humans second. The initial target is technical: email filters checking sender legitimacy, DNS systems translating domain names, and authentication systems verifying identities. By defeating these technical checks, spoofing creates the conditions for human-level deception.
Common spoofing targets include:
- Email authentication systems (SPF, DKIM, DMARC validation)
- DNS servers and domain resolution infrastructure
- Network routing and IP attribution systems
- System authentication and access controls
- Individual email clients displaying sender information
Phishing targets human psychology directly. The goal is to trigger a specific response from a specific type of person. Target selection reflects access and authority:
- Individual consumers (banking, retail, streaming credentials)
- C-suite executives (financial authority, sensitive data access)
- Finance and HR employees (payment processing, payroll control)
- IT administrators (system access, credential reset capabilities)
- Entire industries with shared vulnerabilities (healthcare, finance)
Purpose of the attack
Spoofing’s purpose is to establish credibility and bypass filters, creating the conditions that make a subsequent attack more effective. Spoofed messages reach inboxes that would otherwise filter them. Spoofed identities receive trust that would normally require verification. Specific spoofing goals include:
- Financial gain through misdirected payments
- Data theft through impersonated data requests
- Malware distribution through trusted-appearing attachments
- Unauthorized access through credential theft setup
Phishing’s purpose is to achieve a direct outcome by extracting value from victims:
- Credential harvesting for account access and resale
- Financial theft through fraudulent payments or direct account access
- Identity theft through personal data collection
- Malware deployment through user-initiated downloads
- Corporate espionage through sensitive data exfiltration
Key methods
Spoofing methods are technical and operate at the infrastructure level:
- Email header manipulation to forge From and Reply-To fields
- Domain registration of lookalike addresses (company-inc.com, c0mpany.com)
- DNS cache poisoning to redirect legitimate domain traffic
- IP address spoofing to hide the true network origin
- Caller ID manipulation for phone-based impersonation
Phishing methods are communicative and operate at the human level:
- Fake login pages that replicate legitimate sites pixel-for-pixel
- Malicious links in emails redirecting to credential-capture pages
- Malware-laden attachments disguised as legitimate documents
- Urgent requests exploiting authority and time pressure
- Business email compromise messages impersonating executives or vendors
Detection tips
Spoofing and phishing leave different clues. Spoofing indicators tend to appear in technical details, while phishing warning signs often show up in the tone and content of the message.
Recognizing spoofing:
- Inspect actual sending address beyond displayed name (hover over or click to reveal full address)
- Check for domain variations: missing letters, transposed characters, extra words (company-support.com)
- Verify HTTPS certificates on websites (check the issuing organization, not just the padlock icon)
- Look for domain age inconsistencies (legitimate organizations don’t use recently registered domains)
- Check email headers directly for server origin mismatches
Recognizing phishing:
- Unexpected urgency: “Act immediately,” “Your account will be suspended”
- Generic greetings: “Dear Customer,” “Dear User,” instead of your actual name
- Requests for credentials, payment changes, or sensitive data via email
- Suspicious links where displayed URL text doesn’t match actual destination
- Grammar inconsistencies or slightly off-brand formatting
- Offers that seem too good to be true or threats that seem disproportionate
How Spoofing and Phishing Work Together
Spoofing and phishing are most dangerous when combined: spoofing provides the credibility that makes phishing believable, and phishing provides the financial motive that makes spoofing worth the effort.
The combined attack flow:
- Attacker researches target: Identifies an organization’s executives, vendors, and communication patterns.
- Spoofing creates legitimacy: Registers a lookalike domain or compromises an email account.
- Phishing delivers the hook: Sends a convincing message using the spoofed identity with a specific harmful request.
- Victim acts on trust: Processes a payment, submits credentials, or opens an attachment because the spoofed identity passed initial credibility checks.
- Attacker achieves objective: Captures credentials, receives fraudulent payment, or gains system access.
Example 1: Vendor invoice fraud
An accounts payable employee receives what looks like a routine email from a trusted vendor ([email protected]) saying their banking details have changed. But the real address is [email protected]. One subtle letter swap. Easy to miss. The request seems normal, no one double-checks, and a payment is sent straight to an attacker-controlled account.
Example 2: Executive credential theft
An employee receives an email appearing to come from their CTO directing them to a new company portal requiring immediate credential setup. The spoofed sender address shows the CTO’s real name. The linked page is a pixel-perfect replica of the company’s authentication system. Entered credentials go directly to attackers who use them to access internal systems.
IBM’s analysis of phishing kits found that the information technology sector was the most spoofed industry, with finance and insurance second, reflecting where the combination of spoofing and phishing delivers the highest attacker returns.
How to Prevent Spoofing and Phishing
Effective prevention requires technical controls that address spoofing infrastructure and human controls that address phishing psychology.

Technical controls
Implement DMARC at enforcement policy (p=reject or p=quarantine) to prevent unauthorized messages from using your domain in spoofing attacks. DMARC, combined with SPF and DKIM, creates a technical barrier that stops domain-level spoofing before messages reach recipients.
MFA for email accounts prevents account takeover: the most convincing spoofing method because it uses legitimate accounts. Even when phishing successfully captures passwords, MFA stops attackers from accessing accounts to send spoofed messages from real addresses.
Email filtering platforms that analyze behavioral patterns catch spoofed messages that authentication protocols miss, flagging messages that deviate from normal sending patterns, contain BEC-pattern language, or originate from suspicious infrastructure.
Organizational strategies
Technology can block a large portion of spoofing and phishing attempts, but it cannot replace human judgment. Regular training that teaches employees how to recognize spoofed senders, suspicious domains, and manipulative requests strengthens the one layer attackers still try to exploit. Hands-on simulations, where employees practice spotting and responding to realistic phishing scenarios, tend to be far more effective than passive classroom instruction.
Clear verification procedures also make a measurable difference. Financial requests should always require out-of-band confirmation using trusted contact numbers already on file, not phone numbers or links provided in the message itself. That one safeguard alone can stop most spoofing and phishing schemes that aim to trigger fraudulent payments.
Email list hygiene
Maintaining a clean email list reduces organizational exposure to both threats. Clean lists with validated contacts support accurate sender reputation signals that help security tools identify anomalies. Organizations with strong sender reputation and consistent sending patterns are harder to spoof convincingly. Email list validation removes invalid, risky, and unverifiable addresses that weaken the sending infrastructure, which attackers study when planning spoofing campaigns.
Good security for email marketers combines authentication, validated lists, and ongoing monitoring to create the consistent sending patterns that make spoofing attempts detectable through behavioral analysis.
When to Seek Professional Help
Some spoofing and phishing situations require expert support beyond internal capabilities. Seek professional help when:
- Repeated targeted attacks: If your organization is experiencing ongoing, sophisticated phishing campaigns suggesting persistent attacker interest, security professionals can assess your threat profile and implement targeted defenses.
- Financial loss has occurred: Wire fraud or payment diversion requires immediate engagement with your bank, law enforcement, and potentially forensic security professionals to trace and potentially recover funds.

- Data breach is suspected: If phishing resulted in credential exposure, unauthorized system access, or data exfiltration, incident response professionals should assess the scope and contain damage.
- System compromise is detected: Malware delivered through phishing requires professional remediation to ensure complete removal and identify what was accessed.
- Your domain is being spoofed: If customers or partners are receiving spoofed emails from your domain, DMARC forensics and domain monitoring services can identify attack infrastructure and scope.
Organizations whose contact databases contain invalid, outdated, or risky addresses face elevated exposure because poor list hygiene signals weak email security posture to attackers. DeBounce’s email list validation identifies and removes addresses that weaken sender reputation and increase vulnerability to spoofing campaigns targeting your domain.
The Bottom Line
Spoofing and phishing serve different roles in the attacker’s toolkit, and understanding that difference is what makes defenses effective. Spoofing fakes technical identifiers to bypass filters and build trust; phishing exploits that trust to manipulate victims into harmful actions. Together, they form the most common and costly combination in email-based cybercrime.
Defending against spoofing requires technical controls: DMARC, SPF, DKIM authentication that prevents domain forgery, and MFA that blocks account takeover. Defending against phishing requires human controls: employee training, verification procedures, and behavioral awareness that catches social engineering attempts that technical filters miss.
Check your domain’s DMARC configuration today, and assess your employee training: when did your team last practice identifying a spoofed sender address in a realistic scenario?
Maintain a clean email infrastructure as part of your long-term security and deliverability posture. Use DeBounce to validate contact lists, remove invalid and risky addresses, and maintain the consistent sender reputation that makes spoofing attempts against your domain easier to detect and block. Strong authentication and validated lists together create a foundation that reduces both spoofing and phishing risk across all your email communications.